Malicious code insertion, dependency poisoning, data exfiltration — these are worrisome words to organizations who deliver software products to customers. The complex process of deploying and maintaining software is fraught with supply chain risks, and the likelihood of an attack is higher than ever.
According to Sonatype’s State of Software Supply Chain Report, software supply chain attacks increased at a rate of 742% between 2019 and 2022. Gartner predicts that by 2025, 45% of organizations will have been hit by an attack. A single vulnerability — such as Log4j or Log4Shell — can open up the supply chain to various attacks, ranging from ransomware and malware to data exfiltration and cryptojacking. That’s why mitigating supply chain risks is an absolute must for SaaS organizations.
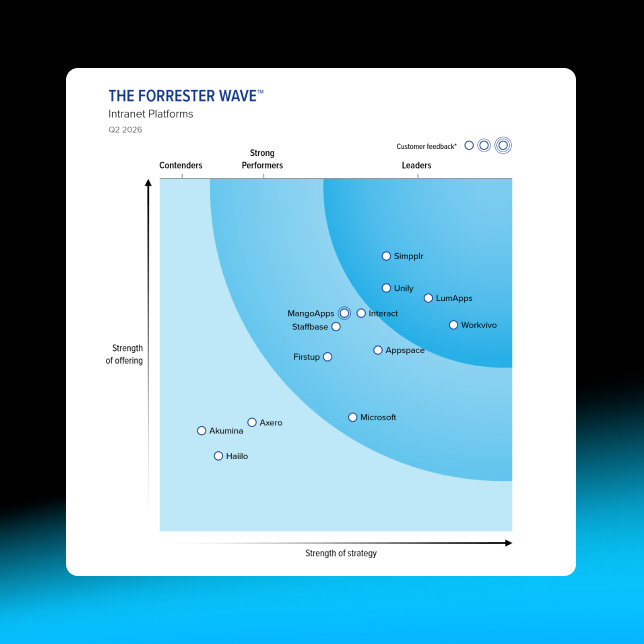
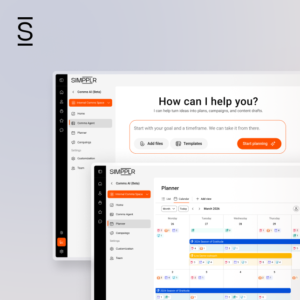
It’s a challenge that Simpplr confronts head-on with industry-leading intranet security.
We’ll go into those details later, but first let’s look at common types of software supply chain attack, along with some real-world examples. We’ll also examine how supply chains become vulnerable, the costs of an attack, and steps your organization can take to harden software supply chain security and reduce your risks.
Get a handle on intranet security best practices
Types of software supply chain attacks
Software supply chain attacks are a category of cyberattacks that target vulnerabilities or weaknesses in the software development and distribution process. These attacks aim to compromise software before it reaches end-users, thereby potentially affecting a large number of systems. Read on for some common types of software supply chain attacks.
Malicious code insertion
In this type of attack, a hacker infiltrates the software development process and inserts malicious code or malware into the software’s source code or build process. The compromised software is then distributed to users, potentially infecting their systems.
For instance, Magecart attacks — when hackers gain access to a server/code via unpatched vulnerabilities and install malware that funnels live payment data to a collection server — have plagued Magento, Adobe Commerce and other ecommerce platforms. Sansec researchers reported last year that as many as 38% of all retail websites running Magento and Adobe Commerce are already infected with malware. But the “holy grail of Magecart client-side fraud is a supply chain attack,” Sensec researchers wrote. “With the press of a button, the attacker can inject its malware, which is now loaded on each and every store. And within seconds, all visitors of said web stores are running the skimming code.” Fortunately, less than 1% of all Magecart incidents in 2021 were supply chain attacks.
Data exfiltration
Data exfiltration is when unauthorized parties gain access to an individual’s or company’s data on a computer or server and copy, transfer, or retrieve it. It can occur through a variety of methods, including malware, phishing, insider threats or any exploitation of security vulnerabilities.
Data exfiltration can be used to steal sensitive data such as customer records, financial information, intellectual property and trade secrets, or to disrupt operations, damage a company’s reputation and extort money. A real-world example of data exfiltration is the cyberattack on Equifax in 2017 — one of the most significant hacks in history due to the scale and sensitivity of the data stolen.
Software backdooring
In this type of attack, bad actors may insert hidden “backdoors” or vulnerabilities into software and gain unauthorized access or control over systems where the compromised software is installed. Backdoored software can be used for espionage or data theft, among other types of attacks.One well-known example is SolarWinds (2020), where cybercriminals inserted a backdoor into the Orion platform’s software updates to gain control of the systems on which the software was installed.
Fake updates
Attackers may create counterfeit software updates or patches and distribute them through fake or compromised update servers. Users, thinking they are installing legitimate updates, unknowingly introduce malware onto their systems. The CCleaner compromise of 2017 is one example. Hackers infiltrated the supply chain of this popular system optimization tool and distributed a malicious version of CCleaner through official channels. Millions of users unknowingly installed this compromised version, which included a backdoor, allowing attackers to gain unauthorized access to affected systems.
Dependency poisoning
Many software projects rely on third-party libraries and dependencies. In a dependency poisoning attack, an attacker compromises a trusted dependency used by a software project, so that when the software is deployed, it includes the malicious code from the poisoned dependency.
An example of a dependency attack is the Apache Struts2 OGNL injection vulnerability (CVE-2017-9802). Discovered in 2017, this vulnerability was exploited by attackers to carry out a number of high-profile attacks, including the Equifax data breach, which affected over 147 million people — the attackers stole sensitive data, including Social Security numbers, credit card numbers, and driver’s license numbers.
Dependency confusion
These automated attacks revolve around internally created dependencies that don’t exist on public open-source libraries. The attacker registers a dependency using the same name as a public repository, only with a higher version number. This version may be pulled into a software build, instead of the internal dependency. Well-known ethical hacker Alex Birsan used dependency confusion to hack into dozens of tech firms and steal more than $130,000 in bug bounty rewards.
Compromised development tools
Attackers may target the tools and development environments used by software developers. For example, they could distribute malicious Integrated Development Environment (IDE) plugins or compromise build servers, infecting software during the development and build stages. A real-world example of compromised development tools involves the attack on the “Node Package Manager” (NPM), a widely used package manager for JavaScript. An attack in December 2021 compromised hundreds of desktop apps and websites with dozens of malicious NPM modules that contained obscure JavaScript code.
Software supply chain interception
In this type of attack, a cybercriminal intercepts legitimate software updates or packages during the distribution process and replaces them with malicious versions. This often involves compromising distribution servers or software repositories.
For example, ShadowPad malware, which has been deployed by the Chinese government-sponsored BRONZE ATLAS threat group since 2017, was found in software updates for a Ukrainian accounting software called MeDoc. Attackers compromised MeDoc’s update servers and distributed malware-laden updates to thousands of organizations. This led to a wide-scale cyberattack known as the NotPetya outbreak.
Compromised certificates
Attackers may steal or forge digital certificates used to sign software packages. Signed software is considered more trustworthy, so attackers use these certificates to sign malicious software, making it appear legitimate. One example is D-Link in 2021, when attackers compromised the digital certificates used by the networking equipment manufacturer. These stolen certificates could have been used to sign malicious software or firmware updates, potentially impacting the security of D-Link’s customers.
Counterfeit software
Hackers may create counterfeit or pirated versions of legitimate software and distribute them through unofficial channels. These counterfeit copies might contain malware or have vulnerabilities. Currently, there are counterfeit Windows installers in circulation which might contain malware or vulnerabilities that can compromise user systems.
Insider threats
Disgruntled employees or contractors within a software development organization can intentionally introduce vulnerabilities or malicious code into the software supply chain.

Causes of supply chain attacks
Several factors can increase the risk of a software supply chain attack. These factors can vary depending on the specific circumstances and vulnerabilities of an organization, but some common risk factors include:
Complexity
As software development becomes increasingly distributed, the software supply chain grows more complex. Each component or dependency introduced into the chain can potentially become a point of vulnerability if not adequately secured.
Dependency on third-party components
Many software projects rely on third-party libraries, frameworks and open-source components. If these components are not regularly updated and audited for security issues, they can introduce vulnerabilities into the software supply chain.
Lack of supply chain visibility
Organizations may lack complete visibility into their software supply chain, making it challenging to identify and mitigate potential supply chain risks. It’s crucial to understand the sources of software components and the relationships between them.
Insufficient code review and testing
Rushed development schedules, resource constraints, or a lack of robust code review and testing processes can result in the introduction of vulnerabilities into the software supply chain. Insufficient testing may fail to catch security issues.
Weak access controls
Weak access controls and authentication mechanisms within the supply chain can allow unauthorized individuals or groups to infiltrate the development environment and compromise the software.
Missed patches and updates
Failure to promptly apply security patches and updates to all components of the software supply chain can leave known vulnerabilities unaddressed.
Lack of security best practices
Failure to implement security best practices throughout the software development lifecycle — such as secure coding standards, vulnerability scanning and penetration testing — can leave software supply chains vulnerable. For example, weaknesses in build and distribution processes can result in insecure build servers, distribution channels and packaging methods. This leaves the door open for hackers to infiltrate and manipulate the software during these critical stages.
Addressing these risk factors requires organizations to adopt a proactive approach to software supply chain security.
It’s critical to implement security controls, regularly audit and monitor the supply chain, conduct security assessments, and foster a culture of security awareness among employees. Collaboration with third-party vendors and partners is also essential to ensure security throughout the supply chain.
Cost of supply chain attacks
Supply chain attacks impact organizations financially, operationally and reputationally.
Financial impact of software supply chain attacks
The financial costs of software supply chain attacks are expected to exceed $46 billion in 2023, according to a study by Jupiter Research. The research found that financial losses tied to software supply chain attacks will increase by 76% by 2026, and government, healthcare, automotive and financial organizations will bear the brunt of these costs.
Direct financial losses include expenses related to data breaches, legal fees and regulatory fines. Indirect financial losses may occur due to business disruptions, downtime and lost revenue — especially if the attack goes undetected for an extended period.
Reputational costs
Reputation damage is another significant cost, as supply chain attacks can erode customer trust and brand equity — resulting in customer churn and decreased sales. Legal and regulatory costs can mount as organizations face lawsuits from affected parties and fines from regulatory authorities.
Operational costs
Operational costs include expenses to remedy supply chain disruptions, find alternative suppliers and expedite shipments. The loss of intellectual property or proprietary information can also have long-term financial repercussions. Additional costs might include customer notification and support expenses, ongoing monitoring and mitigation efforts, increased insurance premiums, and the cost of hiring cybersecurity experts for investigation and forensics.
Ultimately, the true cost of a supply chain attack may not become fully apparent right away, and some consequences — such as reputation damage and customer trust — can have lasting impact. To mitigate these risks, organizations must invest in robust cybersecurity measures, conduct thorough risk assessments, and have effective incident response plans in place.
12 Strategies to reduce supply chain risks
Mitigating supply chain risks from software vendors is crucial for protecting your organization’s security and data integrity. Here are some steps you can take to reduce these risks:
1. Implement Software Development Lifecycle (SDL) practices
Integrate practices and principles into the software development process to ensure that security is a fundamental aspect of the product, from inception to deployment.
Simpplr offers an unparalleled security-first IT infrastructure for corporate intranet services. They incorporate secure development best practices into every phase of the software development lifecycle — from design and coding to testing and deployment. Simpplr developer and cybersecurity teams maintain detailed documentation of secure coding practices and frequently undergo third-party audits or assessments to validate adherence to intranet security best practices. Simpplr’s SLA’s back up these underlying promises to customers worried about the vulnerabilities of their internal networks.
2. Assess your vendors
Be sure to conduct a thorough assessment of all software vendors before entering into contracts. Evaluate their cybersecurity practices, history of security incidents, and compliance with relevant standards and regulations. Once you choose your vendors, Include robust cybersecurity clauses in the contracts. Clearly define security responsibilities, reporting procedures for security incidents and consequences for non-compliance. You may also consider adding provisions for security audits and assessments of vendor systems.
It’s critical to look for industry-leading intranet security when evaluating new providers. Are you asking the right questions? Download Simpplr’s free checklist for guidance.
3. Ensure complete supply chain visibility
Maintain a clear and up-to-date inventory of all software components and dependencies used in your projects, including libraries, frameworks and third-party modules. Be sure to understand the origins and sources of each component, including the organizations or individuals responsible for maintaining them.
4. Establish strict security policies and standards
Enforcing security policies, standards and guidelines for the software supply chain is a critical step. For instance, Simpplr’s production data centers encrypt all incoming and outgoing data via end-to-end with Secure Socket Layer (SSL), so that your data and privacy is protected from unwanted third-party intruders. Simpplr is also one of the few vendors in the Intranet software space to maintain ISO 27001 and SOC 2 certifications for their own operations as well as to require them of their subprocessors.
5. Implement secure coding practices
Ensure that developers adhere to secure coding practices and follow best practices for integrating third-party components. It’s a good idea to use security development tools such as static code analysis and dynamic testing tools to identify and remediate vulnerabilities.
Simpplr developers follow industry-recognized standards and guidelines (OWASP, SANS). They actively work to mitigate common vulnerabilities like SQL injection, cross-site scripting (XSS), and authentication flaws that could jeopardize intranet security. Moreover, Simpplr’s SDLC incorporates rigorous processes for review, testing and patching.
6. Manage dependencies, patches and updates
Regularly update and patch all software components and dependencies to address known vulnerabilities. You should also monitor vulnerability databases and security advisories for updates related to your dependencies.
7. Perform thorough code reviews and testing
Conduct security-focused code reviews to identify vulnerabilities in your software, and implement a robust testing strategy that includes security testing, penetration testing and vulnerability scanning.
8. Enable multi-factor authentication
Implement strong access controls and authentication mechanisms for vendor access to your systems. Use multi-factor authentication (MFA) wherever possible, and restrict vendor access to only the systems and data necessary for their services. For example, Simpplr’s modern intranet software leverages MFA to allow you to control who sees what content and who can create content, using audiences integrated for your HR or identity system.
MFA is usually coupled with SSO (Single Sign-On), which offers a central repository for login activities to enhance security incident detection and response. Administrators can remotely log out users or invalidate sessions if they detect suspicious activity. Simpplr integrates with any SSO system or identity provider that supports SAML 2.0 or OAuth/OIDC 2.0, such as Microsoft Entra ID (formerly Azure Active Directory), Okta and hundreds of other solutions.
9. Apply zero trust principles
NIST Information Technology Laboratory defines zero trust (ZT) as:
“An evolving set of cybersecurity paradigms that move defenses from static, network-based perimeters to focus on users, assets, and resources. A zero trust architecture (ZTA) uses zero trust principles to plan industrial and enterprise infrastructure and workflows. Zero trust assumes there is no implicit trust granted to assets or user accounts based solely on their physical or network location.”
Apply the ZT principles of least privilege across your software supply chain, limiting access and privileges to only what is necessary.
10. Assess risk regularly
Regularly assess the security risks associated with each component in your supply chain, and conduct threat modeling exercises to identify potential vulnerabilities and attack vectors.
Learn more about threat modeling and the supply chain
11. Conduct security awareness training
The best defense is knowledge. To that end, provide ongoing security awareness training for your development teams and other stakeholders, and encourage a security-conscious culture across your organization.
12. Have an incident response plan
Despite your best efforts, an attack may still happen. Be sure to develop and regularly update your incident response plan for detecting, responding to and recovering from supply chain security incidents. Secure backup and recovery should be part of this plan.
Unified data platforms like Simpplr often include data backup and disaster recovery features, ensuring that critical information is protected and can quickly restore in case of security attacks or other events. The foundation of Simpplr’s disaster recovery plan includes geographically separate primary and secondary servers. Simpplr conducts real-time replication to disk at each data center and near real-time replication to disaster recovery centers. This kind of production-driven data center architecture lessens the risk of single points of failure across the entire IT infrastructure.
How Simpplr can help
The importance of proactive software supply chain risk mitigation cannot be understated. Cybercriminals will never rest — and the software supply chain is a prime target. It’s critical to understand the scope of attack vectors and steps you can take to protect your organization.
By taking a proactive approach to mitigating supply chain risk, you’ll reduce the likelihood of security breaches and maintain a more resilient and secure software supply chain.
Risk management of your IT infrastructure is a full-time job. Simpplr’s intranet safeguards continue to maintain the highest level of security protocols to protect their clients from data breaches. Request a demo to learn more.