This article was originally published on February 29, 2024, and was updated on November 18, 2024.
Your company’s intranet system contains a wealth of sensitive information, from employee data to confidential documents and more. Do you know how to protect it? Let’s talk about how to plan and conduct a thorough review. Then you can use the free intranet security review checklist to make sure you got it all.
- 1 The importance of planning intranet security reviews
- 2 The role of compliance in intranet security
- 3 The benefits of regular intranet security reviews
- 4 Preparation for an intranet security review
- 5 Points to address in your intranet security review
- 6 Tips for implementing your intranet security review results
- 7 Proactively assessing intranet security gaps
- 8 Evaluating intranet solutions providers for security and compliance
Let’s get started.
The importance of planning intranet security reviews
Yes, everybody knows that data breaches are bad. Failing security protocols leave organizations open to attacks, data loss, fines and more.
- Within six months of a cyber attack, 60% of small companies close
(Cybersecurity Ventures). - Companies lose an average of $4.45 million after a breach (IBM).
- Ransomware attacks increased by 13% in a single year, more than the previous five years combined (Verizon).
A Cisco survey found that 62% of organizations reported a significant security event in just two years. Breaches were the most common (51%), followed by outages (51%), ransomware events (46%) and DDOS attacks (46%).
A prime example of inadequate protection comes from the Equifax breach. Attackers gained access to internal servers on the company’s corporate network, ultimately exposing the sensitive personal data of almost 150 million people. The event resulted in nearly $700 million in compensation and penalties, as well as congressional hearings, executive firings, and damaged market value along with consumer trust.
Learn how to reduce software supply chain risks
The role of compliance in intranet security
When selecting an intranet platform, it’s critical to assess both security and compliance to protect data, meet regulatory standards, and avoid liabilities. Security ensures strong defenses like encryption and access control, while compliance confirms these align with industry regulations, such as GDPR.
Intranet solutions that meet both standards reduce breach risks, prevent costly legal penalties and help safeguard your organization’s reputation — making these factors essential in vendor selection.
The benefits of regular intranet security reviews
Performing intranet security reviews regularly can help you:
- Detect threats: Identifying and acting promptly on new or overlooked vulnerabilities will close gaps before exploits occur.
- Verify compliance: Governmental regulations and other external directives may change slowly, but they require maintenance, too.
- Update systems: The review process sheds light on aging infrastructure that might need upgrades or replacement to avoid exposure.
- Monitor activity: Ongoing reviews can reveal anomalies that signal the risk of a breach before it happens.
- Strengthen policies: Expert feedback helps you fortify vulnerable processes around access, data management and incident response.
- Safeguard user data: Regular evaluations reassure customers and employees alike that their information is responsibly managed and secured.
- Limit damage: Identifying and resolving security gaps minimizes loss if an incident still manages to occur.
Check out 10 intranet security best practices
Preparation for an intranet security review

Proper preparation makes for a smooth yet comprehensive intranet review strategy. Follow these tips to make this process easier.
1. Assemble the right team
Data shows that having both internal IT staffers and third-party cybersecurity consultants yields the best results. Blend these pros to assess from different viewpoints and skill sets.
Internal team members offer intimate knowledge of organizational specifics — network architectures, controls, past issues and more. And consultants contribute an impartial perspective plus extensive expertise in conducting similar reviews across various industries.
2. Determine the budget and scope
Clarify budget parameters and the review’s scale before starting. Key considerations include:
- Testing: Do you need network scans, penetration tests, facility walkthroughs? Identify which assessments you need to evaluate your intranet’s security.
- Systems: Which hardware and software will you examine? You must consider servers, cloud platforms and more.
- History: Will you analyze system logs, anomaly reports, breach responses, etc., to spot security gaps or improvement areas? Looking at past patterns can uncover future risks.
3. Choose the right framework
An unstructured review is better than none, but an established framework can act as a guide. Using globally recognized benchmarks lends credibility as well as structure to your efforts.
Popular options for intranet security reviews are:
NIST Cybersecurity Framework (CSF)
The National Institute of Standards and Technology CSF provides a methodology for checking threat prevention, data protection, attack detection, and response.
CIS Critical Security Controls
The Center for Internet Security Critical Security Controls (CIS Controls) are a prioritized set of safeguards to mitigate the most prevalent cyber-attacks against systems and networks.
CSA Cloud Controls Matrix (CCM)
The Cloud Security Alliance CCM is composed of 197 control objectives covering all key aspects of cloud technology. It can be used as a tool for the systematic assessment of a cloud implementation such as an intranet.
Any of these frameworks supports systematically examining security.
4. Set the timeline
To ensure you get enough information without impeding daily operations, you might need to schedule four to 12 weeks for your review, depending on the environment’s intricacy. You’ll need to run interviews, schedule scans, present findings, and implement recommendations.
5. Select the right tools
Specialized tools automate data gathering and testing for faster, more comprehensive reviews. Some of the leading options include:
- Network vulnerability scanners like Nessus (or the free version, Nessus Essentials) and OpenVAS to probe systems for flaws
- Penetration testing tools such as Metasploit for safe attack simulation
- Password analyzers to check for weak credentials
- Policy management platforms to simplify analysis and more
Points to address in your intranet security review
Now that you know what you need to start, let’s go over what you need to check.
User management
- Evaluate all systems and applications tied to the intranet.
- Match access limitations to seniority levels, job functions, user roles, etc.
- Verify that security protocols meet current standards, such as password length and variation.
- Check for and deprovision unused staff accounts.
Critical security features
- Enable role-based access control (RBAC) to ensure users can only access information relevant to their roles.
- Implement multi-factor authentication (MFA) to add an extra layer of security and mitigate risks associated with compromised passwords, especially for high-risk accounts.
- Consider secure, email-less access for frontline employees without corporate email addresses, using alternative authentication methods like SMS codes or secure tokens.
Centralizing these functions with a single-sign-on (SSO) or Identity and Access Management (IAM) system can help. Look for a system that supports SCIM 2.0, which enables automatic user provisioning and, importantly, deprovisioning on termination. Your intranet should also offer granular role-based access control (RBAC), which limits system permissions to an employee’s duties.
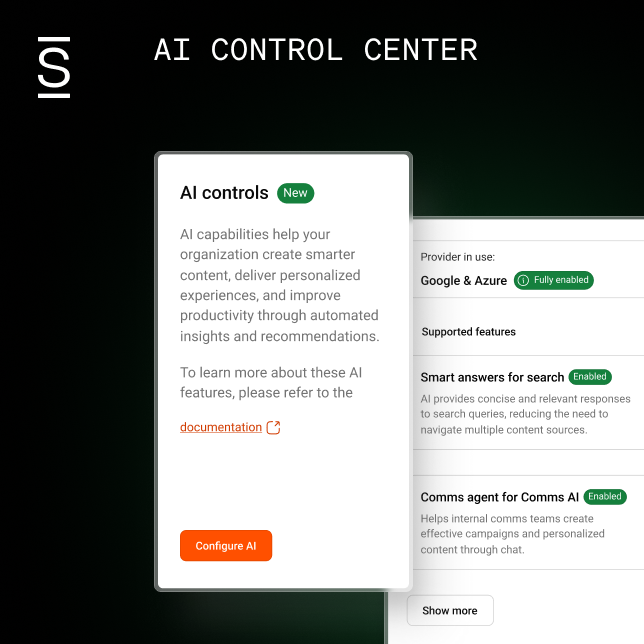
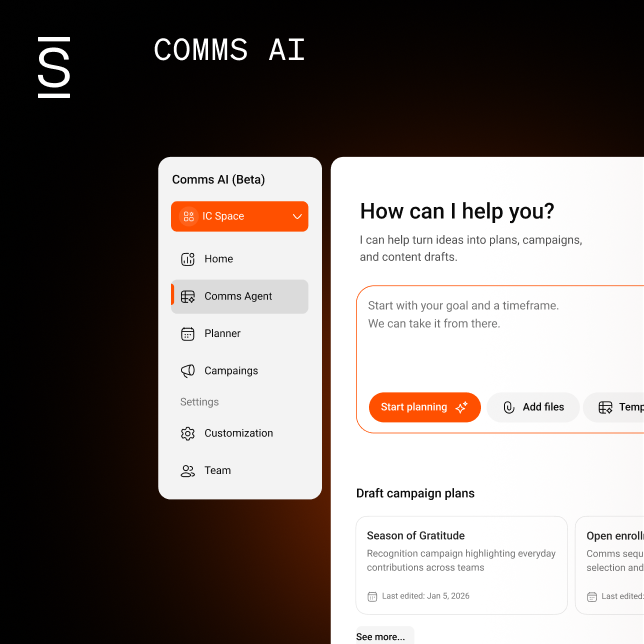
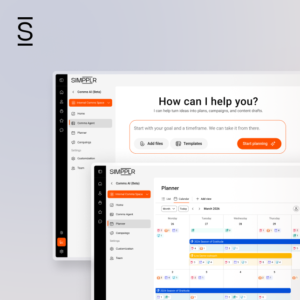
For example, the Simpplr intranet platform incorporates RBAC, supports SCIM, and integrates to more than 100 SSO/IAM applications, including Microsoft Entrata (formerly Azure AD), Okta, OneLogin and Ping Identity.
SSO enables users to log in just once to access multiple applications. RBAC limits what a user can do. SCIM ensures employees who leave the company no longer have access. These features offer a host of benefits:
- Enhancing security through centralized session management
- Aligning access to functionality based on user roles
- Reducing vulnerability by eliminating unnecessary accounts
Employees enjoy the convenience of one login, and you avoid the stress of extra permissions that could lead to misuse or theft.
Check out Simpplr customer reviews and testimonials.
Here’s why automated user provisioning matters
Data handling and storage
To improve your intranet security, you’ll want to do the following:
- Classify data sensitivity and protection requirements as per regulations like GDPR. A unified intranet platform centralizes storage, allowing tighter controls and encryption.
- Map regulated data locations across the infrastructure. Simpplr’s architecture allows fewer points of attack by consolidating communication, collaboration and data.
- Confirm that storage aligns with security and compliance prerequisites. Combining aspects of internal comms on one platform will make protections comprehensive.
With Simpplr’s classification and mapping, you can safely transfer and maintain all types of data.
Coding practices
Review source code of custom applications and integrations using standards like OWASP Top 10 and SANS Top 25 to check for exposures. Simpplr developers follow these industry standards to mitigate common vulnerabilities.
Also, analyze authentication, input validation, output encoding, etc. to ensure code-level security. Simpplr incorporates rigorous SDLC processes for security reviews, testing and patching.
Simpplr developers actively work to reduce common vulnerabilities like SQL injection, cross-site scripting (XSS) and authentication flaws that could jeopardize intranet security.
Data transmission
- Review how data travels through workstations, servers and cloud platforms. Simpplr protects client data using end-to-end encryption.
- Enable comprehensive encryption-in-transit via SSL/TLS versions that support strong cryptography to prevent intercepted data during transmissions. Simpplr mandates TLS 1.2+ or higher.
- Use AES-256 or stronger protections for encryption-at-rest of stored data. Simpplr leverages FIPS 140-2 Level 3 certified cryptography modules.
Anomaly detection and reporting
Cyber threats evolve quickly, so anomaly detection is crucial to identify security incidents. You’ll need:
- Heuristic analysis to recognize suspicious activity and configurations that signal threats even before signatures are available
- Machine learning and artificial intelligence to find anomalies and attack patterns by analyzing vast volumes of network traffic and event data
- Behavior analysis that tracks irregularities indicative of malware or insider risks
Examining recent intranet breaches and their consequences highlights the real-world importance of proactive anomaly detection and robust incident response processes. Lapses in security can lead to significant financial losses and reputational damage.
Robust security information and event management (SIEM) and security operations center (SOC) solutions should also be evaluated.
- Review event data capture and correlation to validate enterprise-wide visibility.
- Examine threat parameters and alerts so personnel can investigate issues quickly.
- Confirm incident-response details like anomaly investigation and threat validation as well as mitigation, recovery and reporting procedures.
Carefully inspecting detection and response processes lets you locate and contain threats with less business disruption. And ensure that any cloud software providers maintain strong threat controls and risk management. For example, Simpplr proactively monitors usage to rapidly detect risks of insider threats or compromised accounts.
Policies, protocols and awareness
- Review all formal policies and protocols around access controls, acceptable use standards, data ownership, etc.
- Make sure policies outline detailed response and recovery processes for security incidents.
- Examine policy gaps discovered in prior breaches to ensure they’ve been addressed.
- Gauge end-user understanding by surveying staff on core protocols.
Security and compliance ratings
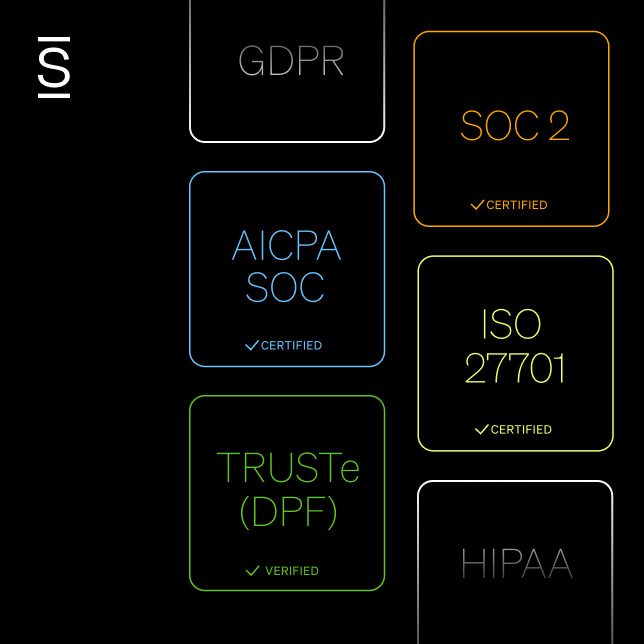
Familiarize yourself with security and compliance certifications related to your intranet environment. Common examples include:
- ISO 27001/27002: Internationally recognized standards for information security management systems (ISMS). Simpplr maintains ISO 27001 certification, reducing risk across people, processes and systems.
- SOC 2: Service Organization Control 2 reports to cover factors like security, confidentiality, processing integrity and availability. Simpplr undergoes SOC 2 Type 2 audits annually to confirm strong controls in these areas.
- GDPR: The European Union’s General Data Protection Regulation laws governing data privacy. Simpplr participates in the TRUSTe Data Privacy Verification program, including annual audits to comply with GDPR requirements.
- WCAG / VPAT: The Web Content Accessibility Guidelines (WCAG) establish standards for digital accessibility. Simpplr maintains a competitive Voluntary Product Accessibility Template (VPAT), demonstrating conformance to WCAG 2.2 AA standards and ensuring accessibility for all users, including those with disabilities.
Determine which apply best to your circumstances, then establish or ensure that these certifications remain active via regular independent audits. For Simpplr, annual ISO 27001 and SOC 2 audits validate continuous, effective policies and controls to safeguard intranet data.
Performance
Factor availability, speed and scalability into the review:
- Uptime/availability: Review system and application availability percentages. Simpplr uses physically separated, isolated data centers connected via low-latency, high-throughput, redundant networking. Application services, file storage and databases automatically failover across zones without interruption. Simpplr provides Service Level Agreements (SLA) that guarantee 99.9% uptime.
- Speed: Review page load and lag times when accessing apps/files. Simpplr maintains speed through load-balancing across database replicas. As user demand increases, read replicas increase to prevent performance problems. Similarly, Simpplr utilizes a content delivery network (CDN) to speed page delivery.
- Scalability: Does performance stay consistent amid more users, locations and data demands? Simpplr’s cloud infrastructure auto-scales computing, memory, and storage to match usage peaks and growth. Multiple data centers provide redundancy while read replicas accommodate capacity constraints.
Simpplr combines multi-datacenter failover, automated backup/restore, database replication and load balancing to ensure reliable data availability and performance.
Scalability and growth
Review architecture and capacity planning to leave room to smoothly scale amid predictable expansion like more staff, offices, M&A activity, etc.
As a cloud-based provider, Simpplr’s intranet platform is infinitely scalable to match client growth trajectories.
Consider upcoming projects that will require security transitions like cloud migrations, new app integrations, intranet modernization, etc. Simpplr’s secure data centers guarantee service uptime and bandwidth suitable for rapid scaling.
Incident response
- Interview IT staff on protocols if the intranet is compromised. Platforms like Simpplr have built-in disaster recovery infrastructure, including replication and geographically separate servers.
- Initiate sample breach scenarios, then assess the response. Simpplr uses production-level data centers with replication, minimizing single points of failure risk.
- Identify successes like quickly detecting simulated attacks and engaging protocols. Simpplr’s architecture enables efficient data recovery so end-users can restore previous versions.
- Pinpoint areas of improvement such as communication delays. Conducting disaster recovery testing is the best practice for security.
Unified platforms like Simpplr provide robust backup and restoration capabilities through real-time replication across geographically diverse data centers. Testing these processes ensures critical data remains protected and quickly recoverable after a cyber attack.
Tips for implementing your intranet security review results
The real value of your intranet security review stems from using its results to continually strengthen protections. Now you can efficiently allocate resources for the following:
- Patching exposed OS, software and firewall vulnerabilities
- Upgrading authentication mechanisms and access controls
- Migrating from insecure legacy systems, networks or cloud platforms
- Increasing encryption measures
- Expanding staff training on updated security protocols
- Tightening procedures based on lessons learned
Additional considerations:
- Break major initiatives into milestones for smoother execution.
- Outline how findings will improve security and reduce risk to gain executive buy-in.
- Make a roadmap to schedule future reviews after remediation.
Proactively assessing intranet security gaps
In digital security, proactive intranet security reviews are essential rather than optional. You must:
- Detect emerging threats early before major exploits
- Continually evolve protections aligned to new risk trends
- Reassure employees that their data is responsibly secured
- Allow partners to safely access and collaborate within the network
- Empower leadership to pursue initiatives with lower liability
By addressing security and compliance requirements up front, intranet platforms can provide a secure foundation for innovation, allowing teams to focus on growth with confidence that their data is protected.
Consistent evaluations balance innovation with responsible protection.
They surface crucial upgrades to policies, protocol, and systems to improve your security as conditions continue to change.
As threats intensify, ensure your environment can safely enable digital transformation through modern information architecture. Get your free intranet security review checklist to get started.
Evaluating intranet solutions providers for security and compliance
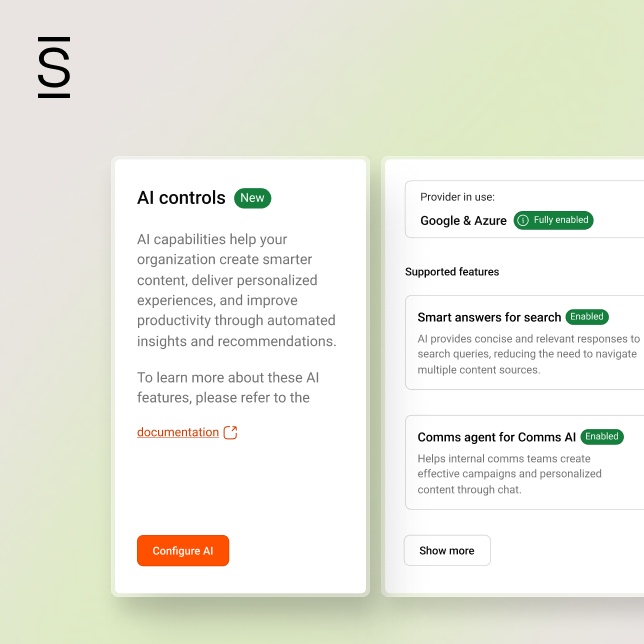
When evaluating intranet solutions, it’s essential to prioritize security and compliance features. Look for solutions that offer core protections like single sign-on (SSO), role-based access control (RBAC), end-to-end encryption, and compatibility with standards such as GDPR.
A platform that integrates advanced anomaly detection and incident response capabilities can help minimize risks from both internal and external threats. Additionally, ensure your provider has a proven track record with independent security certifications like ISO 27001 and SOC 2.
For a comprehensive overview of selecting the right intranet platform for your organization, Simpplr’s Intranet Buyer’s Guide 2025 provides an in-depth look at key security features and compliance factors to consider. Whether you’re upgrading your current system or evaluating new solutions, this resource can help you make a more informed choice that aligns with your organization’s security needs.